Malware analysis is a critical skill for cybersecurity professionals, threat hunters, and incident responders.
With the growing sophistication of cyber threats, having access to reliable, free malware analysis tools is essential for dissecting, understanding, and mitigating malicious software.
This article reviews the 10 best free malware analysis tools in 2025 covering their specifications, features, reasons to use, and who they’re best for.
.png
)
Whether you’re a beginner or a seasoned analyst, these tools will help you break down malware samples and enhance your cyber defense strategies.
SEO Keywords
Primary SEO Keywords: malware analysis tools, free malware analysis, best malware analysis tools, malware analysis 2025
Secondary SEO Keywords: cyber threats, cybersecurity tools, malware detection, malware sandbox, malware removal tools, malware analysis online, network security, threat intelligence
Comparison Table: 10 Best Free Malware Analysis Tools (2025)
1. Cuckoo Sandbox

Cuckoo Sandbox is an open-source automated malware analysis platform that enables analysts to execute and observe suspicious files in a controlled virtual environment.
It supports a wide range of file types and provides detailed behavioral reports, making it a staple for malware researchers.
Specifications:
OS: Windows, Linux
Analysis: Static & Dynamic
API: Yes
Deployment: On-premise
Features:
Modular and extensible architecture
Analyzes executables, documents, scripts, and more
Tracks API calls, network traffic (including SSL/TLS), and file system changes
Integrates with Volatility for memory analysis
Generates comprehensive, high-level reports
Reason to Buy:
Completely free and open-source
Highly customizable for advanced workflows
No reliance on third-party cloud—full data control
✅ Best For: Automated sandboxing and custom malware analysis workflows
🔗 Try Cuckoo Sandbox here → Cuckoo Sandbox Official Website
2. REMnux
.webp)
REMnux is a Linux toolkit specifically designed for malware analysis and reverse engineering.
It comes preloaded with hundreds of community-vetted tools, allowing analysts to dissect malicious code without the hassle of manual setup.
Specifications:
OS: Linux (x86/amd64, OVA, Docker)
Analysis: Static & Dynamic
API: No
Deployment: Local, Cloud
Features:
Pre-configured with tools for unpacking, deobfuscation, and network forensics
Beginner-friendly with extensive documentation
Easily updatable via SaltStack
Can be deployed in the cloud or on-premise
Reason to Buy:
Saves time with pre-installed, curated tools
Free and open-source
Suitable for both beginners and experts
✅ Best For: Reverse engineering and comprehensive malware analysis
🔗 Try REMnux here → REMnux Official Website
3. VirusTotal
.webp)
VirusTotal is a web-based malware scanning service that leverages dozens of antivirus engines and online tools to analyze suspicious files and URLs.
It’s a fast, easy way to get a second opinion on potential threats.
Specifications:
OS: Web-based
Analysis: Static (some dynamic)
API: Yes
Deployment: Cloud
Features:
Scans files, URLs, IPs, and domains
Aggregates results from multiple AV engines
Provides hash, network, and behavior analysis
Offers public and private submissions
Machine learning-based detection
Reason to Buy:
No installation required
Extremely fast and user-friendly
API for automation and integration
✅ Best For: Quick online malware detection and threat intelligence
🔗 Try VirusTotal here → VirusTotal Official Website
4. Hybrid Analysis
.webp)
Hybrid Analysis by CrowdStrike offers a free, cloud-based sandbox for in-depth malware analysis.
It uses AI-driven behavior scoring and supports both public and private submissions, making it accessible for individuals and teams.
Specifications:
OS: Web-based
Analysis: Static & Dynamic
API: Yes
Deployment: Cloud
Features:
AI-powered behavioral scoring
Detailed forensic reports
Supports a wide range of file types
Integration with CrowdStrike Falcon
Minimal setup required
Reason to Buy:
Fast, cloud-based analysis
Public and private modes for confidentiality
Easy integration with security platforms
✅ Best For: Cloud-based sandbox analysis and enterprise integration
🔗 Try Hybrid Analysis here → Hybrid Analysis Official Website
5. ANY.RUN

ANY.RUN is an interactive, real-time malware analysis sandbox that lets you manually interact with malware samples during execution.
Its intuitive web interface and collaboration features make it popular among security researchers.
Specifications:
OS: Web-based
Analysis: Static & Dynamic
API: Yes
Deployment: Cloud
Features:
Real-time, interactive analysis
Monitors processes, network traffic, and system changes
Collaboration tools for team analysis
Supports Windows malware
Reason to Buy:
Live interaction with malware for deeper insights
Easy to use, no installation needed
Facilitates collaborative investigations
✅ Best For: Interactive, real-time malware analysis
🔗 Try ANY.RUN here → ANY.RUN Official Website
6. PEStudio

PEStudio is a lightweight Windows tool for static analysis of executable files. It quickly reveals suspicious indicators, such as packed sections, imports, and embedded resources, without running the file.
Specifications:
OS: Windows
Analysis: Static
API: No
Deployment: Local
Features:
Analyzes PE files for anomalies
Detects obfuscation, suspicious imports, and indicators of compromise
No installation required (portable)
Reason to Buy:
Fast, efficient static analysis
Great for triaging large numbers of samples
Freeware
✅ Best For: Static analysis of Windows executables
🔗 Try PEStudio here → PEStudio Official Website
7. Process Monitor (ProcMon)
.webp)
Process Monitor (ProcMon) is a Windows system monitoring tool that records real-time file system, registry, and process/thread activity.
It’s essential for observing how malware interacts with the operating system.
Specifications:
OS: Windows
Analysis: Dynamic
API: No
Deployment: Local
Features:
Monitors and logs system calls
Filters and highlights suspicious activity
Exports logs for further analysis
Reason to Buy:
Deep visibility into malware behavior
Free and widely trusted
No installation required
✅ Best For: Monitoring system activity during malware execution
🔗 Try Process Monitor here → ProcMon Official Website
8. Wireshark

Wireshark is the world’s most popular network protocol analyzer, enabling analysts to capture and inspect network traffic generated by malware in real time.
Specifications:
OS: Windows, Linux, Mac
Analysis: Dynamic (Network)
API: No
Deployment: Local
Features:
Captures and analyzes live network traffic
Supports hundreds of protocols
Filters and decodes suspicious communications
Exports PCAP files for sharing
Reason to Buy:
Essential for analyzing C2 and exfiltration traffic
Free and open-source
Cross-platform support
✅ Best For: Network traffic analysis and threat hunting
🔗 Try Wireshark here → Wireshark Official Website
9. Ghidra

Ghidra is a powerful open-source reverse engineering suite developed by the NSA. It supports disassembly, decompilation, and analysis of binaries across multiple platforms.
Specifications:
OS: Windows, Linux, Mac
Analysis: Static (Reverse Engineering)
API: Yes (Scripting)
Deployment: Local
Features:
Disassembles and decompiles binaries
Supports scripting for automation
Handles complex malware samples
Reason to Buy:
Free alternative to expensive commercial tools
Highly extensible and scriptable
Supports a wide range of architectures
✅ Best For: Advanced reverse engineering of malware binaries
🔗 Try Ghidra here → Ghidra Official Website
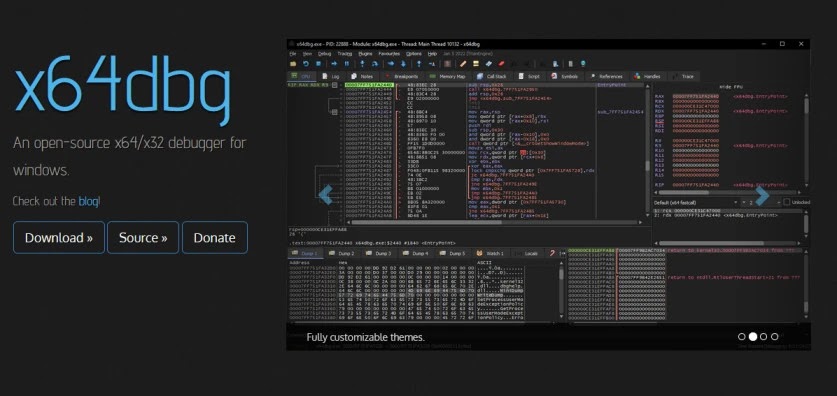
10. x64dbg
.webp)
x64dbg is a free, open-source debugger for Windows binaries. It’s designed for malware analysts and reverse engineers who need to step through code and uncover hidden behaviors.
Specifications:
OS: Windows
Analysis: Static (Debugging)
API: No
Deployment: Local
Features:
User-friendly GUI for debugging
Supports both x86 and x64 binaries
Plugin support for extended functionality
Reason to Buy:
Free, modern alternative to OllyDbg
Powerful for unpacking and analyzing packed malware
Community-driven development
✅ Best For: Debugging and unpacking Windows malware
🔗 Try x64dbg here → x64dbg Official Website
Conclusion
These top 10 free malware analysis tools provide a comprehensive toolkit for anyone tasked with breaking down malware samples in 2025.
From automated sandboxes and static analyzers to advanced reverse engineering suites, each tool brings unique strengths to the fight against cyber threats.
Integrate them into your workflow to stay ahead of evolving malware and protect your organization’s digital assets.