A new wave of ClickFix attacks is abusing highly realistic fake Windows Update screens and PNG image steganography to secretly deploy infostealing malware such as LummaC2 and Rhadamanthys on victim systems.
The campaigns rely on tricking users into manually running a pre-staged command, turning simple social engineering into a multi-stage, file-light infection chain that is hard for traditional defenses to spot.
ClickFix is a social engineering technique in which a web page convinces users to press Win+R, then paste and run a command that has been silently copied to the clipboard.
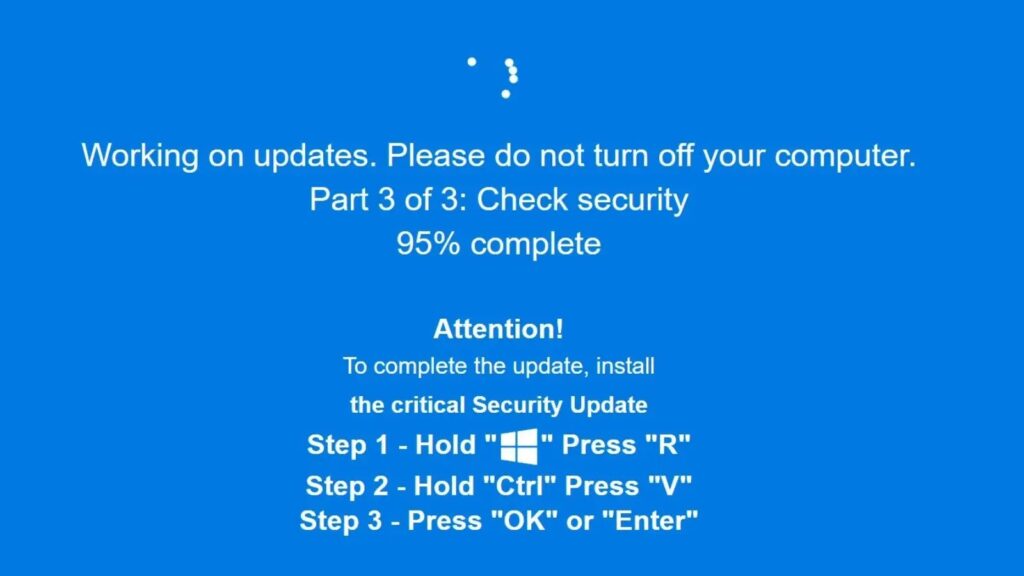
Earlier lures posed as “Human Verification” or robot-check pages, but newer activity observed by Huntress swaps this for a full-screen, blue Windows Update-style splash screen with convincing progress messages.

Once the fake update “completes,” the page instructs users to follow the familiar pattern and execute the malicious Run-box command.
That command typically launches mshta.exe with a URL whose second IP octet is hex-encoded, kicking off a staged chain that downloads obfuscated PowerShell and reflective .NET loaders. This approach leans heavily on trusted “living off the land” binaries, making the activity blend in with legitimate Windows behavior.
Malware hidden in PNG pixels
The most distinctive feature of this campaign is its use of a .NET steganographic loader that hides shellcode inside the pixel data of a PNG image.
Instead of appending data, the loader AES-decrypts an embedded PNG resource, reads the raw bitmap bytes, and reconstructs shellcode from a specific color channel, using a custom XOR-based routine to recover the payload in memory.
The recovered shellcode is Donut-packed and then injected into a target process such as explorer.exe via dynamically compiled C# code that calls standard Windows APIs like VirtualAllocEx, WriteProcessMemory, and CreateRemoteThread.
In analyzed cases, this final stage has delivered LummaC2 and, in a separate Windows Update cluster, the Rhadamanthys information stealer.

Huntress has tracked ClickFix Windows Update clusters since early October, noting repeated use of the IP address 141.98.80[.]175 and rotating paths such as /tick.odd, /gpsc.dat, and /one.dat for the first mshta.exe stage.
Subsequent PowerShell stages have been hosted on domains like securitysettings[.]live and xoiiasdpsdoasdpojas[.]com, pointing back to the same backend infrastructure.
These campaigns continued to appear around the time of Operation Endgame 3.0, which targeted Rhadamanthys’ infrastructure in mid-November, disrupting servers and seizing domains linked to the stealer.
Even after the takedown announcement, researchers observed multiple active domains still serving the Windows Update ClickFix lure, though the Rhadamanthys payload itself appeared to be unavailable.
Because the attack hinges on user interaction with the Run dialog, one strong control is to disable the Windows Run box via Group Policy or registry settings (for example, configuring the NoRun policy under the Explorer key).
Security teams should also use EDR telemetry to watch for explorer.exe spawning mshta.exe, powershell.exe, or other scripting binaries with suspicious command lines.
User awareness remains critical: employees should be trained that neither CAPTCHA checks nor Windows Update processes will ever require pasting commands into the Run prompt from a web page.
During investigations, analysts can further validate potential ClickFix abuse by reviewing the RunMRU registry key, which records recent commands executed via the Run dialog.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.